OVERVIEW
First discovered in May, WastedLocker ransomware is a relatively new strain from the group known as Evil Corp, which was previously associated with the Dridex banking Trojan and BitPaymer ransomware. This ransomware group was brought to our attention with the recent ransomware attack against Garmin. In our research, we discovered why these targeted attacks are even harder to defend against. Read on to learn what to look for and how to avoid this new strain.
RANSOMWARE DETAILS
WastedLocker attacks start with a drive-by compromise to gain initial entry. The attackers use the SocGholish framework to hack legitimate websites that display fake software update alerts to visitors. Attempting to download these fake alerts will deliver PowerShell scripts onto the user’s device, which subsequently download Cobalt Strike. Cobalt Strike then allows the attackers to gain access, move laterally through the target’s network, and deliver the WastedLocker ransomware to the victim host.
Before deploying the ransomware, the attackers perform the following tasks within the target’s network:
- Escalates privileges via UAC bypass method
- Disables Windows Defender
- Gathers information about victim’s environment
- Performs credential dumping
WastedLocker attackers have also been observed in previous attacks to utilize living-off-the-land (LOFT) tools to perform tasks. For example, using the Windows Sysinternals tool PsExec to disable Windows Defender, using PowerShell and WMIC to profile the target’s environment.
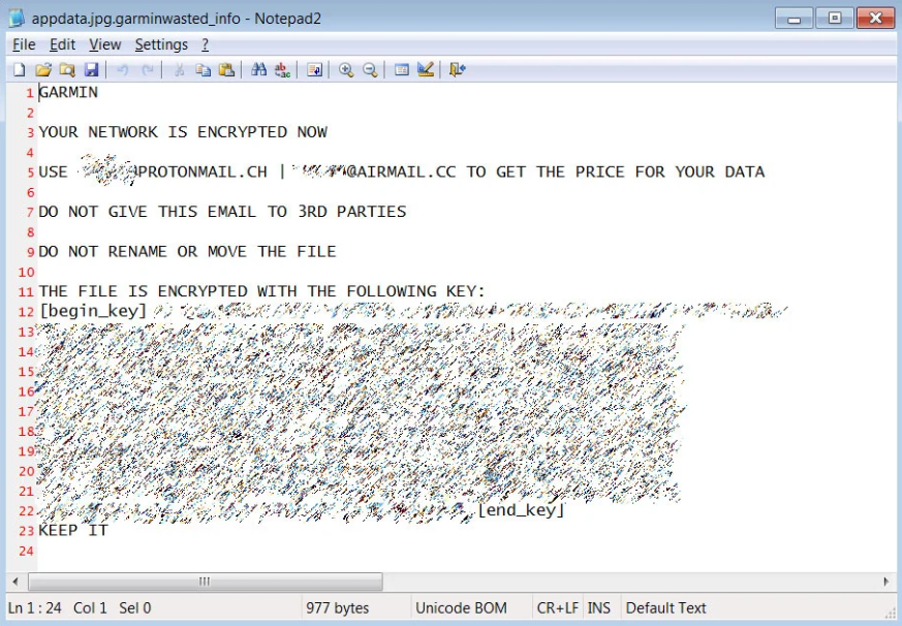
Upon successful encryption of a victim’s file, the ransomware appends a file extension that is a combination of the target organization’s name and the string “wasted”. In the case of the Garmin attack, the file extension “.garminwasted” was appended to encrypted files. For each encrypted file, the ransomware also creates a ransom note with the same name appended with “_info” at the end of the file extension, such as “.garminwasted_info”.
Aside from encryption, the WastedLocker ransomware is also capable of deleting Windows shadow copies to wipe backups and file snapshots to make recovery impossible.
The method of payment provided to decrypt WastedLocker is to contact one of the emails listed within the ransom notes. As of now, email addresses that have been used by the attackers are can belong to either ProtonMail, Eclipso, Tutanota, or Airmail.
Unlike many other ransomwares this year, WastedLocker ransomware does not steal victims’ files but simply encrypt them. However, it is worth noting that WastedLocker attacks are highly targeted and ransomware samples used are each customized for the target organization. This means that standard IOCs such as the file hashes of previous samples would not be very helpful or useful in detections.
PRECAUTIONARY MEASURES
Prevention is better than cure. It is advisable to safeguard you and your organization to avoid being the next victim of this ransomware attacks. We would recommend organization to consider the following measures.
- Keep your anti-virus software / EDR solutions and other security tools installed on the systems updated for detection and prevention from the spread of ransomware.
- Make use of a managed EDR service to quickly react and contain any ransomware vendor
- Managed EDR services can also play a big part in monitoring and alerting on attacked vectors used as a distribution method
- Have a cold or distributed backup system in place, or at minimum have backups separate from production systems, for your critical files or systems.
- Keeping your operating systems up to date on the latest security patches.
- Make use of network segmentation alongside the zero-trust model.
- Close unnecessary network ports to reduce entry points for attackers.
- Apply content filters on email gateways and email systems to prevent malicious content from reaching users and reduce the chance of a possible compromise.
- Educate your employees and users to improve cybersecurity awareness.
ABOUT PROFICIO
Proficio’s Managed, Detection and Response (MDR) solution surpasses the capabilities of traditional Managed Security Services Providers (MSSPs). Our MDR service is powered by next-generation cybersecurity technology and our security experts partner with you to become an extension of your team, continuously monitoring and investigating threats from our global networks of security operations centers. Learn More About Proficio’s Services
REFERENCES
- https://research.nccgroup.com/2020/06/23/wastedlocker-a-new-ransomware-variant-developed-by-the-evil-corp-group/
- https://symantec-enterprise-blogs.security.com/blogs/threat-intelligence/wastedlocker-ransomware-us
- https://www.bleepingcomputer.com/news/security/new-wastedlocker-ransomware-distributed-via-fake-program-updates/
- https://www.bleepingcomputer.com/news/security/dozens-of-us-news-sites-hacked-in-wastedlocker-ransomware-attacks/
- https://www.bleepingcomputer.com/news/security/garmin-outage-caused-by-confirmed-wastedlocker-ransomware-attack/
- https://labs.sentinelone.com/wastedlocker-ransomware-abusing-ads-and-ntfs-file-attributes/